-
Notifications
You must be signed in to change notification settings - Fork 10.1k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Microsoft Security Advisory: iOS12 breaks social, WSFed and OIDC logins #4647
Comments
|
The anti-forgery cookie is set as "Lax" by default. Do we have to change there too? I don't have an iOS device here to test and confirm. services.AddAntiforgery(options =>
{
options.Cookie.SameSite = SameSiteMode.None;
}); |
|
@fabiano there's indication yet that Antiforgery is affected as it's not usually used during a remote authentication flow. |
|
@Tratcher yes, you are right. Thanks. |
|
FYI this Webkit update also affects Safari on MacOS Mojave. |
|
We made the SameSiteMode.None cookie change in an ASP.net Core 2.1 Razor Pages project. This fixed part of the problem on iOS 12. (The user is no longer stuck in a login loop.) However if a non-logged in user goes directly to a protected resource and logs in they are redirected to “/“ after login instead of the referring protected page. Has anyone else encountered this issue or have suggestions? This only happens on iOS 12 so far. |
|
@rdellar please open a separate issue with the details for your scenario. |
|
"Apple have stated they believe their change is correct behavior, and that the fault lies in every other browser's implementation." Classic Apple. |
|
the suggested fix is not working when using Azure AD with ASPNET CORE 2.0. am I missing a configuration? |
|
@thdotnet In asp.net core 2.1 it works. I don't specify |
|
Did the same and it’s not working for me.
…On Mon, 26 Nov 2018 at 13:14 lucachecchinasarva ***@***.***> wrote:
@thdotnet <https://github.com/thdotnet> In asp.net core 2.1 it works. I
don't specify
app.UseCookiePolicy(new CookiePolicyOptions
{
MinimumSameSitePolicy = SameSiteMode.None,
});
—
You are receiving this because you were mentioned.
Reply to this email directly, view it on GitHub
<https://github.com/aspnet/Security/issues/1864#issuecomment-441673769>,
or mute the thread
<https://github.com/notifications/unsubscribe-auth/ABWP2mu5mCrvR_xLUwUp4VAKhi3QEeHLks5uzAVXgaJpZM4W_dL1>
.
|
|
got help from @Tratcher services.ConfigureApplicationCookie(options => |
|
Hi! |
|
SameSite was never implemented for .NET Framework so why do you need a workaround? |
|
That's ASP.NET Core, not ASP.NET.... the workarounds above should apply. |
|
So i've tried the above suggestions without much luck. Here's the code with the first solution. Am i missing anything? |
|
You're going to need IdentityServer specific guidance. See IdentityServer/IdentityServer4#2595 (comment). They've also addressed it in a later release (IdentityServer/IdentityServer4#2661). |
|
FYI, here's a different approach to solving this issue, while being able to use same-site cookies. |
|
It's sad that the Microsoft-blames-Safari issue has no link to a test. Just trying to reverse analyze the issue from the text of the "security advisory" makes me think that the failures in authentication may occur due to one of the following reasons.
|
|
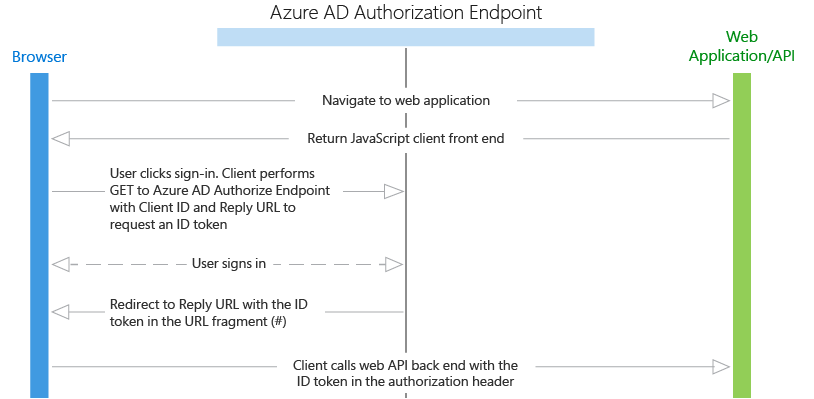
Hi, would any of you know of a way to implement the sameSite cookie workaround in a javascript Single Page App (SPA) doing authentication with Azure Active Directory (AAD) using the ADAL.js library as per the flow described here? Thank you, |
I added SameSiteMode.None in multiple areas. There are no changes in ios devices. This is a Razor Pages app with dotnet core 2.2 if that helps. |
|
Before finding what "works for me", can I reproduce what did not work for anyone? |
I created a new .net core 2.2 Razor Pages Web Application from Visual Studio 2017 with organizational authentication (work or school accounts) through Azure AD. After the site was published with IIS, on ios devices it would prompt users to login to the application but loop infinitely once credentials were entered. Solution from @blowdart did not fix the issue. Once I set AzureADDefaults CookieScheme to none, it has not hit that loop again. |
|
I see this issue is still open, was any fix every implemented or are we just supposed to remove all of the security protection associated with SameSite cookie mode? I find it hard to believe that this is the only solution available. If it is, it's quite disappointing that we need to apply this insecure workaround and rely on anti forgery CSRF checks. Not to say that it isn't important to also implement those checks. Just sad to see that only a workaround was found and no action is being taken aside from that. |
|
iOS's non-conformant implementation has significantly undermined the usefulness of the SameSite standard. There have been a few proposed mitigations for AspNetCore but we don't have any concrete plans at this time. |
|
To this day I did not see a test or a sample project that clearly demonstrates a reproducible failure. I noticed that humans tend to enter heated debates when complexity of issues increases. |
Above code works for me as well. Thank guys all. You save my life! These code bring me to another issue
|
|
As same site is now going to be broken by google in other ways, closing, and a new discussion issue will open when the support for the Chrome same-site updates arrives. |

Microsoft Security Advisory: iOS12 breaks social, WSFed and OIDC logins
Executive summary
Microsoft is releasing this security advisory to provide information about an incompatibly between iOS12 and some types of authentication. This advisory also provides guidance on what developers can do to remove current security restrictions added by ASP.NET to their applications to become compatible with iOS12.
Announcement
The original announcement for this issue can be found at aspnet/Announcements#318
Discussion
Discussion for this issue can be found at https://github.com/aspnet/Identity/issues/1984 for ASP.NET Core Identity
Advisory FAQ
What has changed
The recent iOS12 update has changed Safari's handling of SameSite cookies. The SameSite attribute allows a developer to control when cookies are sent to a web site, enabling the flow to only occur when requests are from the same site. This standard was introduced to reduce exposure to Cross Site Request Forgery (CSRF) attacks. By default ASP.NET Core 2.0 and later protects its authentication cookies using the SameSite property. The change on Apple's part is not limited to ASP.NET Core applications, it is affecting multiple frameworks and authentication software which relay on HTTP forms in a browser, for example authenticating to a third party via Facebook, Twitter or browser based Open ID Connect (OIDC) mechanism.
Apple have stated they believe their change is correct behavior, and that the fault lies in every other browser's implementation.
While we take no stance on the correctness of browser behavior we feel that removing the SameSite protections would expose our customers, and their customers to a wider risk, as it would remove the protection provided everywhere, for all users, in any browser.
How do I know if I am affected?
If your users can no longer login to your web application on iOS12 using Safari then you are affected.
How do I fix this?
Developers can allow iOS12 Safari users to log into their applications by turn off SameSite protection in
ConfigureServices().If you are using ASP.NET Core Identity you disable the protection by configuring cookies with the following code
If you are using cookie authentication without ASP.NET Core identity you can turn off the protection with the following code
If you are using external OIDC providers you may be able to avoid the issue by changing the response mode your provider uses from a POST to a GET request, using the following code. Not all providers may support this.
_Note that in making these changes protection is removed for all users and all browsers. You should ensure that all your actions that make state changes are protected with CSRF anti-forgery mechanisms built into ASP.NET Core.
Rebuilding your application
After making these configuration changes you rebuild your application, test, and redeploy.
Other Information
Reporting Security Issues
If you have found a potential security issue in .NET Core, please email details to [email protected]. Reports may qualify for the .NET Core Bug Bounty. Details of the .NET Core Bug Bounty including terms and conditions are at https://aka.ms/corebounty.
Support
You can ask questions about this issue on GitHub in the .NET Core or ASP.NET Core organizations. These are located at https://github.com/dotnet/ and https://github.com/aspnet/. The Announcements repo for each product (https://github.com/dotnet/Announcements and https://github.com/aspnet/Announcements) will contain this bulletin as an issue and will include a link to a discussion issue. You can ask questions in the discussion issue.
Disclaimer
The information provided in this advisory is provided "as is" without warranty of any kind. Microsoft disclaims all warranties, either express or implied, including the warranties of merchantability and fitness for a particular purpose. In no event shall Microsoft Corporation or its suppliers be liable for any damages whatsoever including direct, indirect, incidental, consequential, loss of business profits or special damages, even if Microsoft Corporation or its suppliers have been advised of the possibility of such damages. Some states do not allow the exclusion or limitation of liability for consequential or incidental damages so the foregoing limitation may not apply.
External Links
Bug 188165 - iOS 12 Safari breaks ASP.NET Core 2.1 OIDC authentication
Revisions
V1.0 (September 28, 2018): Advisory published.
The text was updated successfully, but these errors were encountered: